Understanding Password-Cracking
Techniques
We get daily tons of requests regarding password cracking,
hereby we present a well researched comprehensive article adressing the same
It may bounce many of ur heads but we are sure a must mug up for Geeks nour regular visitors!!
so Gear Up! Dont give up before having a look on the entire article!
Many hacking attempts start with attempting to crack passwords. Passwords are the key piece
of information needed to access a system. Users, when creating passwords, often select passwords
that are prone to being cracked. Many reuse passwords or choose one that’s simple—such
as a pet’s name—to help them remember it. Because of this human factor, most password cracking
is successful; it can be the launching point for escalating privileges, executing applications,
hiding files, and covering tracks. Passwords may be cracked manually or with automated tools
such as a dictionary or brute-force method, each of which are covered later in this chapter.
Manual password cracking involves attempting to log on with different passwords. The
hacker follows these steps:
1.
Find a valid user account (such as Administrator or Guest).
2.
Create a list of possible passwords.
3.
Rank the passwords from high to low probability.
4.
Key in each password.
5.
Try again until a successful password is found.
A hacker can also create a script file that tries each password in a list. This is still considered
manual cracking, but it’s time consuming and not usually effective.
Boring!! isnt it!! A more efficient way of cracking a password is to gain access to the password file on a system.
Most systems
hash
(one-way encrypt) a password for storage on a system. During the
logon process, the password entered by the user is hashed using the same algorithm and then
compared to the hashed passwords stored in the file. A hacker can attempt to gain access to
the hashing algorithm stored on the server instead of trying to guess or otherwise identify the
password. If the hacker is successful, they can decrypt the passwords stored on the server.
Passwords are stored in the Security Accounts Manager (SAM) file on a
Windows system and in a password shadow file on a Linux system.
Understanding the LanManager Hash
Windows 2000 uses NT Lan Manager (NTLM) hashing to secure passwords in transit on the
network. Depending on the password, NTLM hashing can be weak and easy to break. For
example, let’s say that the password is
123456abcdef
. When this password is encrypted with
the NTLM algorithm, it’s first converted to all uppercase:
123456ABCDEF
. The password is
padded with null (blank) characters to make it 14 characters long:
123456ABCDEF__
. Before
the password is encrypted, the 14-character string is split in half:
123456A and BCDEF__.
Each string is individually encrypted, and the results are concatenated:
123456A = 6BF11E04AFAB197F
BCDEF__ = F1E9FFDCC75575B15
The hash is
6BF11E04AFAB197FF1E9FFDCC75575B15
Hacking Tools
Legion automates the password guessing in NetBIOS sessions. Legion scans multiple
IP address ranges for Windows shares and also offers a manual dictionary attack tool.
NTInfoScan is a security scanner for NT 4.0. This vulnerability scanner produces an HTMLbased
report of security issues found on the target system and other information.
L0phtCrack is a password auditing and recovery package distributed by @stake software,
which is now owned by Symantec. It performs Server Message Block (SMB) packet captures
on the local network segment and captures individual login sessions. L0phtCrack contains
dictionary, brute-force, and hybrid attack capabilities.
John the Ripper is a command-line tool designed to crack both Unix and NT passwords. The
cracked passwords are case insensitive and may not represent the real mixed-case password.
KerbCrack consists of two programs: kerbsniff and kerbcrack. The sniffer listens on the network
and captures Windows 2000/XP Kerberos logins. The cracker can be used to find the
passwords from the capture file using a brute force attack or a dictionary attack.
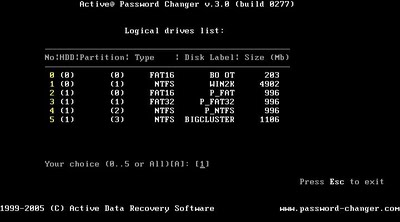
Cracking Windows 2000 Passwords
The SAM file in Windows contains the usernames and hashed passwords. It’s located in the
Windows\system32\config
directory. The file is locked when the operating system is running
so a hacker can’t attempt to copy the file while the machine is booted to Windows.
One option for copying the SAM file is to boot to an alternate operating system such as
DOS or Linux with a boot CD. Alternately, the file can be copied from the
repair
directory.
If a systems administrator uses the RDISK feature of Windows to back up the system, then a
compressed copy of the SAM file called
SAM._
is created in
C:\windows\repair
. To expand
this file, use the following command at the command prompt:
C:\>expand sam._ sam
After the file is uncompressed, a dictionary, hybrid, or brute-force attack can be run against
the SAM file using a tool like L0phtCrack.
Redirecting the SMB Logon to the Attacker
Another way to discover passwords on a network is to redirect the Server Message Block
(SMB) logon to an attacker’s computer so that the passwords are sent to the hacker. In order
to do this, the hacker must sniff the NTLM responses from the authentication server and trick
the victim into attempting Windows authentication with the attacker’s computer. A common
technique is to send the victim an e-mail message with an embedded hyperlink to a fraudulent
Hacking Tools
Win32CreateLocalAdminUser is a program that creates a new user with the username and
password
X
and adds the user to the local administrator’s group. This action is part of the
Metasploit Project and can be launched with the Metasploit framework on Windows.
Offline NT Password Resetter is a method of resetting the password to the administrator’s
account when the system isn’t booted to Windows. The most common method is to boot to
a Linux boot CD and then access the NTFS partition, which is no longer protected, and change
the password.
SMB server. When the hyperlink is clicked, the user unwittingly sends their credentials over
the network.
SMB Redirection
Several automated hacking tools can implement SMB redirection:
SMB Relay MITM Attacks and Countermeasures
An SMB relay MITM attack is when the attacker sets up a fraudulent server with a relay
address. When a victim client connects to the fraudulent server, the MITM server intercepts
the call, hashes the password, and passes the connection to the victim server.
Figure 4.1 illustrates an example of such an attack.
Hacking Tools
SMBRelay is an SMB server that captures usernames and password hashes from incoming
SMB traffic. SMBRelay can also perform man-in-the-middle attacks.
SMBRelay2 is similar to SMBRelay but uses NetBIOS names instead of IP addresses to
capture usernames and passwords.
pwdump2 is a program that extracts the password hashes from a SAM file on a Windows system.
The extracted password hashes can then be run through L0phtCrack to break the passwords.
Samdump is another program to extract NTLM hashed passwords from a SAM file.
C2MYAZZ is a spyware program that makes Windows clients send their passwords as clear
text. It displays usernames and their passwords as users attach to server resources.
SMB relay countermeasures include configuring Windows 2000 to use SMB signing, which
causes it to cryptographically sign each block of SMB communications. These settings are
found under Security Policies/Security Options.
NetBIOS DoS Attacks
A NetBIOS Denial of Service (DoS) attack sends a NetBIOS Name Release message to the NetBIOS
Name Service on a target Windows systems and forces the system to place its name in conflict
so that the name can no longer be used. This essentially blocks the client from participating in the
NetBIOS network and creates a network DoS for that system.
Password-Cracking Countermeasures
The strongest passwords possible should be implemented to protect against password cracking.
Systems should enforce 8–12 character alphanumeric passwords. The length of time the same
password should be used is discussed in the next section.
To protect against cracking of the hashing algorithm for passwords stored on the server,
you must take care to physically isolate and protect the server. The systems administrator can
use the SYSKEY utility in Windows to further protect hashes stored on the server hard disk.
The server logs should also be monitored for brute-force attacks on user accounts.
A systems administrator can implement the following security precautions to decrease the
effectiveness of a brute-force password-cracking attempt:
1.
Never leave a default password.
2.
Never use a password that can be found in a dictionary.
Hacking Tools
SMBGrind increases the speed of L0phtCrack sessions on sniffer dumps by removing duplication
and providing a way to target specific users without having to edit the dump files manually.
The SMBDie tool crashes computers running Windows 2000/XP/NT by sending specially
crafted SMB requests.
NBTdeputy can register a NetBIOS computer name on a network and respond to NetBIOS
over TCP/IP (NetBT) name-query requests. It simplifies the use of SMBRelay. The relay can be
referred to by computer name instead of IP address.
Hacking Tools
NBName can disable entire LANs and prevent machines from rejoining them. Nodes on a Net-
BIOS network infected by the tool think that their names are already in use by other machines.
3.
Never use a password related to the host name, domain name, or anything else that can
be found with whois.
4.
Never use a password related to your hobbies, pets, relatives, or date of birth.
5.
Use a word that has more than 21 characters from a dictionary as a password.
This subject is discussed further in the section “Monitoring Event Viewer Logs.”
In the following sections, we’ll look at two measures you can take to strengthen passwords
and prevent password-cracking.
Password Change Interval
Passwords should expire after a certain amount of time so that users are forced to change
their passwords. If the password interval is set too low, then users will forget their current
passwords; as a result, a systems administrator will have to reset users’ passwords frequently.
On the other hand, if passwords are allowed to be used for too long, then security
may be compromised. The recommended password-change interval is every 30 days. In
addition, it’s recommended that users not be allowed to reuse the last three passwords.
You cannot completely block brute-force password attacks if the hacker
switches the proxy server where the source packet is generated. A systems
administrator can only add security features to decrease the likelihood that
brute-force password attacks will be useful.
Monitoring Event Viewer Logs
Administrators should monitor Event Viewer logs to recognize any intrusion attempts either
before they take place or while they’re occurring. Generally, several failed attempts are logged
in the system logs before a successful intrusion or password attack. The security logs are only
as good as the systems administrators who monitor them.
Tools such as VisualLast aid a network administrator in deciphering and analyzing the
security log files. VisualLast provides greater insight into the NT event logs so the administrator
can assess the activity of the network more accurately and efficiently. The program is
designed to allow network administrators to view and report individual users’ logon and
logoff times; these events may be searched according to time frame, which is invaluable to
security analysts who are looking for intrusion details.
The event log located at
c:\\windows\system32\config\Sec.Event.Evt
contains the
trace of an attacker's brute-force attempts.